“Taxonomy is described sometimes as a science and sometimes as an art, but really it’s a battleground.”
After attending a cyber-risk accumulation workshop with a variety of cyber risk underwriters, I was moved to spend my morning walks thinking hard about cyber risk accumulation. Where does it accumulate and how?
This led me to sketch out a quick and dirty taxonomy for underwriters to consider. Time and temporality feature heavily in my thinking process, so I want to caveat that this is a snapshot of where we are today, not a timeless taxonomy.
- Hidden and uncontrollable
- Technology
- SITEs/Vendors
- Semi-uncontrollable but not hidden to insurers paying out
- Occurrences/Attackers
- Litigation
- Controllable and not hidden
- Policies and exclusions
Hidden and uncontrollable
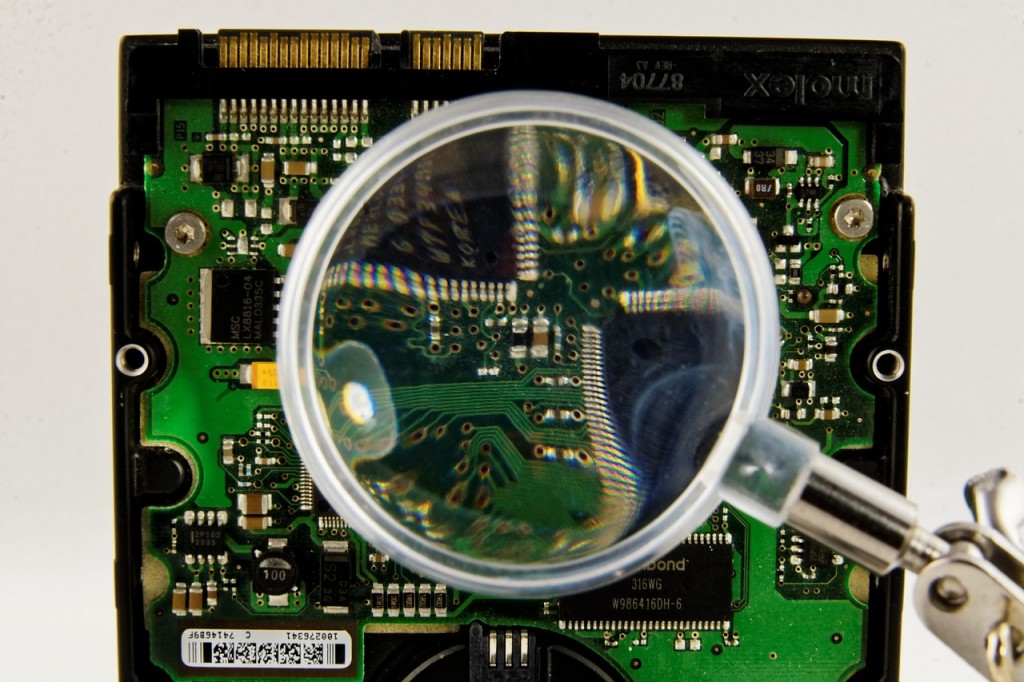
Some elements of understanding potential risk accumulation are currently hidden from insurers; by and large, what software, technology or vendors their policy holders use is a mystery to them. They may ask in questionnaires about operating systems employed by a business but this is just the tip of the iceberg when it comes to the full catalogue of technology utilised by an organisation. In fact, the questionnaire proves the point: they have to ask for this information to be revealed from the insured.
Additionally, technology can embed within other technology and updates constantly change the state of security. The vendors of vendors are also a problem and are often hidden to underwriters. Like Leonard E. Read’s essay I, Pencil, we do not know who made the TCP stack in every device in a given company nor what compiler version was used to compile it. It is near impossible to build a fully comprehensive, multi-limbed, ever-branching list of all the temporal technologies employed in the purview of a certain company; a close-to-complete list at one moment will almost immediately be rendered out-of-date.
Semi-uncontrollable but not hidden to insurers paying out
What is more knowable is the incidence or occurrence of attack and if there is litigation with respect to a insurance policy. I can hear my hacker-brethren screaming at that last sentence, shouting that you cannot always know when you’ve been compromised. A stealthy attacker can persist for years without being detected. My point is, simply, that prevalence of attack matters less to insurers than occurrences which trigger policies. They only pay out the policies that claim and are concerned with risk accumulation said claiming policies. So, in that microcosm, they know which policies are paying out and who has been attacked. So, why do I suggest these two elements are semi-controllable?
Insurers can choose to fight or accept litigation and, likewise, they can battle attackers via incident response teams and security companies on retainer. They can also choose to reduce vulnerability through wise application of an underwriter’s trade tools but that is a blog post for another time.
Controllable and not hidden
The last category of policies and exclusions has existed for hundreds of years and traditionally is seen as the most controllable option for managing accumulations risks.
So what can we infer from this?
Funding anything that makes technology and supply chain dependencies more transparent is worthwhile, especially if it eliminates the slow or laboured request for data and simply derives it directly from a reliable source. Finding new ways to control or influence litigation or to thwart attackers will help everyone lower the cost of policies and allow the market to grow.
The essential take-away from this blog for underwriters is to think hard about what you don’t know, what you want to know and how much it will cost you to find out. Don’t chase data that is instantly out of date. Instead, find out which data is relevant to accumulation studies empirically. Control the risks you can, and accept the ones you can’t.
Build your own taxonomy of accumulation attractors for cyber as a thought experiment over coffee or tea. Then blog about them or post them in our comments to promote discussion.
Thanks for reading.



Martin Huddleston
Dear Eireann,
I’m interested in the topic here. However out of curiosity did you ever write the blog to explain “They can also choose to reduce vulnerability through wise application of an underwriter’s trade tools but that is a blog post for another time.”?
Kind regards
Martin Huddleston
Eireann Leverett
I absolutely think these risks can be controlled in the way you describe. How this is done is open to many debates and approaches. Perhaps it is another blog post, and I’ll get to it!
The prevailing approach I hear today though, is: Let’s model it, then we’ll understand the risk and be done. The “active” approach to risk management for cyber is still not very popular as an approach. Coming from the security community, we have plenty of methods of doing so, but less of scientific rigour about what is effective. This is what I hope to see more of in the future.
Eireann Leverett
I guess it is time for another blog post. 😀